If you feel overwhelmed by Kubernetes, would like to get a better overview, or perhaps don’t know all the resources it makes available, you are not alone. Many in the Compliant Kubernetes community have asked for a secure way to have a graphical user interface. Either in addition to or instead of the command-line tooling. We are happy to announce that the Lens project provides exactly that, and that it is entirely compatible with Compliant Kubernetes. Both in terms of technology and in terms of security.
Setup is quick and easy, and you can get started right away!
What is Lens and how does it work?
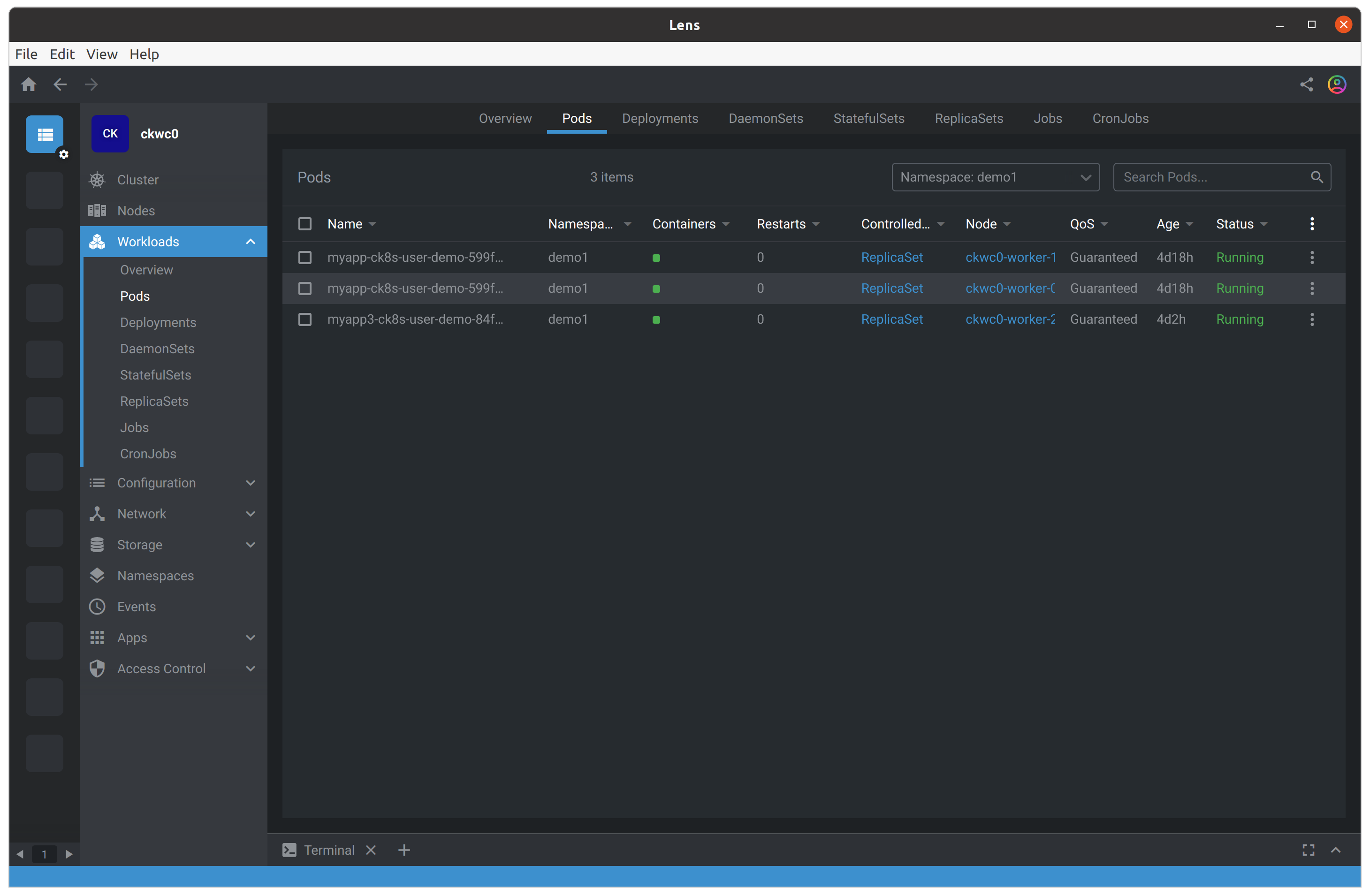
Lens is an attractive Kubernetes user interface that works solely with your user permissions. That means that there are no components to install in the cluster. And, in turn, it does not require more permissions than your user account already has.
Because it works entirely on your computer, it does not reduce your Compliant Kubernetes cluster’s security posture one bit. You can regard it as a graphical tool that builds up its views using Kubernetes API calls just the way that kubectl does. So it can only make API requests you could have made yourself, but Lens does it for you.
Lens also integrates with Helm. That means you can use it to install and manage your Helm-deployed applications, making the entire process simple and smooth. Simply add your Helm repositories as usual, head over to your “Apps” section, and you can start managing your deployed releases of Helm Charts.
How do I get started?
We have recently added step-by-step instructions for how to install and configure Lens for your Compliant Kubernetes cluster. In short, the steps are:
- Install Lens from the Lens project’s website.
- Connect to your Compliant Kubernetes cluster, with full OpenID Connect support via the authentication component (Dex).
- Optionally, configure the Kubernetes Namespaces you want Lens to interact with, because your user account does not have access to them all.
The instructions work both for paying customers of the Elastisys Compliant Kubernetes managed service, and for users of the open source Kubernetes distribution.
Users that self-host Compliant Kubernetes can also enable Prometheus integration. Until this can be done in a way that does not compromise the security of the cluster, this cannot be done for users of the managed service. We’re keeping up on this as the technology develops.

